Page 243 - CA Final PARAM Digital Book.
P. 243
- Drones
5. Assessing the complexity of the IT environment: Understand that IT applications vary in complexity based
on factors like automation, reliance on system reports, customization, business model, yearly changes, and
emerging technology adoption. Assess the overall complexity of the IT setting.
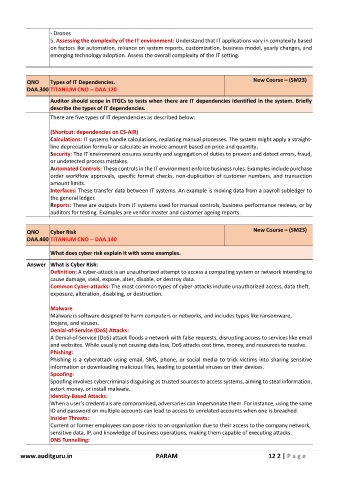
QNO Types of IT Dependencies. New Course – (SM23)
DAA.300 TITANIUM CNO -- DAA.120
Auditor should scope in ITGCs to tests when there are IT dependencies identified in the system. Briefly
describe the types of IT dependencies.
There are five types of IT dependencies as described below:
(Shortcut: dependencies on CS-AIR)
Calculations: IT systems handle calculations, replacing manual processes. The system might apply a straight-
line depreciation formula or calculate an invoice amount based on price and quantity.
Security: The IT environment ensures security and segregation of duties to prevent and detect errors, fraud,
or undetected process mistakes.
Automated Controls: These controls in the IT environment enforce business rules. Examples include purchase
order workflow approvals, specific format checks, non-duplication of customer numbers, and transaction
amount limits.
Interfaces: These transfer data between IT systems. An example is moving data from a payroll subledger to
the general ledger.
Reports: These are outputs from IT systems used for manual controls, business performance reviews, or by
auditors for testing. Examples are vendor master and customer ageing reports.
QNO Cyber Risk New Course – (SM23)
DAA.400 TITANIUM CNO -- DAA.140
What does cyber risk explain it with some examples.
Answer What is Cyber Risk:
Definition: A cyber-attack is an unauthorized attempt to access a computing system or network intending to
cause damage, steal, expose, alter, disable, or destroy data.
Common Cyber-attacks: The most common types of cyber-attacks include unauthorized access, data theft,
exposure, alteration, disabling, or destruction.
Malware
Malware is software designed to harm computers or networks, and includes types like ransomware,
trojans, and viruses.
Denial-of-Service (DoS) Attacks:
A Denial-of-Service (DoS) attack floods a network with false requests, disrupting access to services like email
and websites. While usually not causing data loss, DoS attacks cost time, money, and resources to resolve.
Phishing:
Phishing is a cyberattack using email, SMS, phone, or social media to trick victims into sharing sensitive
information or downloading malicious files, leading to potential viruses on their devices.
Spoofing:
Spoofing involves cybercriminals disguising as trusted sources to access systems, aiming to steal information,
extort money, or install malware.
Identity-Based Attacks:
When a user's credentials are compromised, adversaries can impersonate them. For instance, using the same
ID and password on multiple accounts can lead to access to unrelated accounts when one is breached.
Insider Threats:
Current or former employees can pose risks to an organization due to their access to the company network,
sensitive data, IP, and knowledge of business operations, making them capable of executing attacks.
DNS Tunnelling:
www.auditguru.in PARAM 12.2 | P a g e